The Trust Stack Is Broken
Every small professional-services firm runs on a hidden trust protocol. A client calls with urgent payment instructions. The receptionist recognizes the voice, glances at the caller ID, and routes the request. A paralegal hears familiar details and drafts the wire. A staff accountant sees an email that looks right and sounds right, so they act.

That protocol worked for decades. It stopped working in 2024. Voice phishing attacks surged 442% between the first and second halves of the year, according to CrowdStrike's 2025 Global Threat Report. By early 2025, deepfake-enabled vishing had exploded another 1,600% quarter over quarter. McAfee found that three seconds of audio is enough to produce a voice clone with 85% accuracy. In September 2025, researchers at Queen Mary University of London published findings in PLOS One confirming that voice cloning had crossed the "indistinguishable threshold": human listeners can no longer reliably tell a cloned voice from the real person.
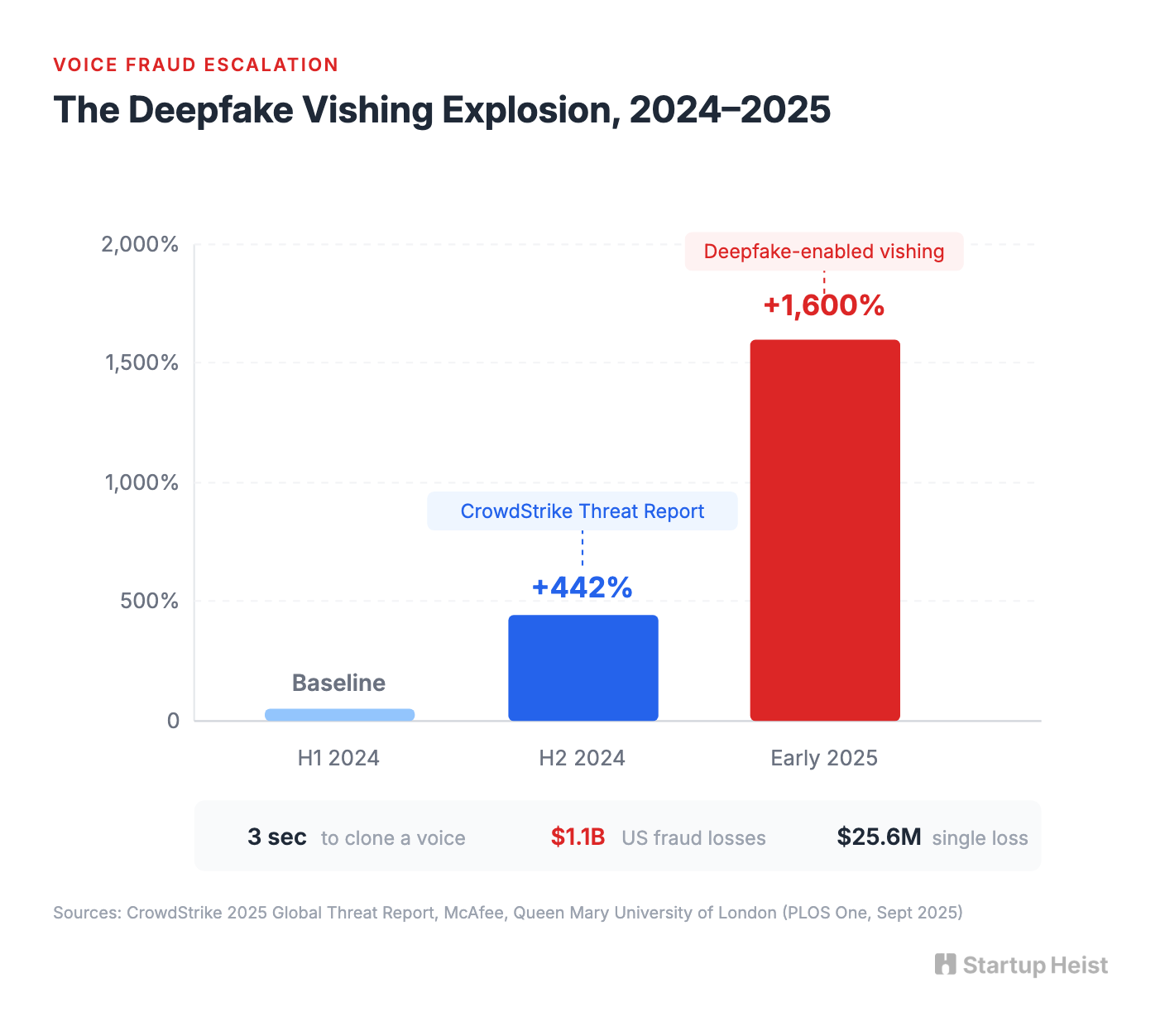
Deepfake-related fraud losses in the United States hit $1.1 billion in 2025, tripling from the year before. An engineering firm at Arup lost $25.6 million after a deepfake video conference led staff to execute 15 wire transfers across five separate accounts. Small firms are the softest targets: lean staff, minimal verification procedures, and high-trust client relationships where questioning someone's identity feels socially awkward.
Nothing has replaced the old protocol yet.
The money: 200 firms at $120/month average = $24K MRR. Median wire fraud loss is $72,000, so the product sells itself.
Inside:
• Full MVP scope and tech stack
• CPA-first go-to-market playbook
• Tiered pricing with real unit economics
• Four compounding moats to build early
The infrastructure to fix this already exists. Biometric identity verification and liveness detection is a $14.2 billion global market, projected to reach $26.8 billion by 2031. Vendors package passive, active, and adaptive liveness checks as standard features, priced between $0.50 and $3.00 per verification. Confirming a live human on a phone screen is mature, cheap, and available off the shelf.
The Product Nobody Has Packaged
The major identity verification vendors sell horizontal infrastructure to fintechs, marketplaces, and large regulated businesses. Onfido (now part of Entrust), Jumio, Persona, Veriff, Identomat, and others all assume integration projects, developer teams, monthly minimums, and workflow design capacity. Persona's lowest tier starts at $250 per month. Jumio builds custom pricing packages. Even when the raw per-check price is reasonable, the surrounding product assumes a buyer with a compliance department or at least a developer who knows what an API is.
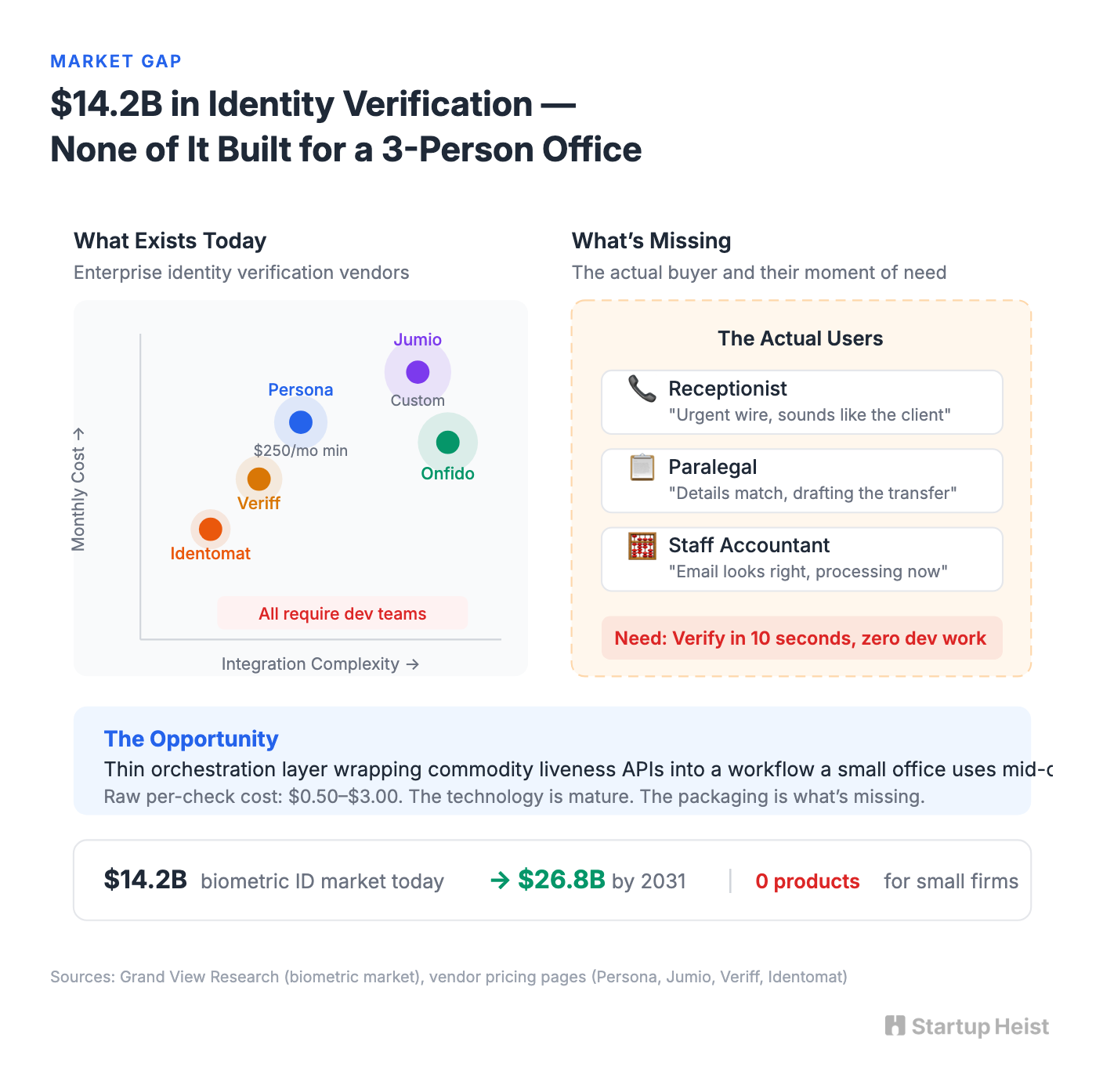
The actual buyer here is a receptionist, paralegal, or staff accountant. The moment that matters is not onboarding; it's mid-relationship re-verification before a risky action. The UX requirement is dead simple: send a link from your phone in ten seconds. What's missing is a thin orchestration layer wrapping commodity liveness infrastructure into a workflow a three-person office can use during a tense client call.
Why CPAs First
The United States has roughly 46,000 to 51,000 CPA firms. About 86% have fewer than ten employees. They routinely handle sensitive payment instructions, tax document releases, entity changes, and elderly clients. The Journal of Accountancy published a direct warning in April 2026 about AI-enabled fraud targeting older clients through CPA relationships. The profession is already primed to take this seriously, and CPAs are culturally process-driven. They're accustomed to checklists, audit trails, and policy language. Selling them "this is now part of procedure" is easier than selling it to a law office where adoption depends on one partner feeling the pain personally.
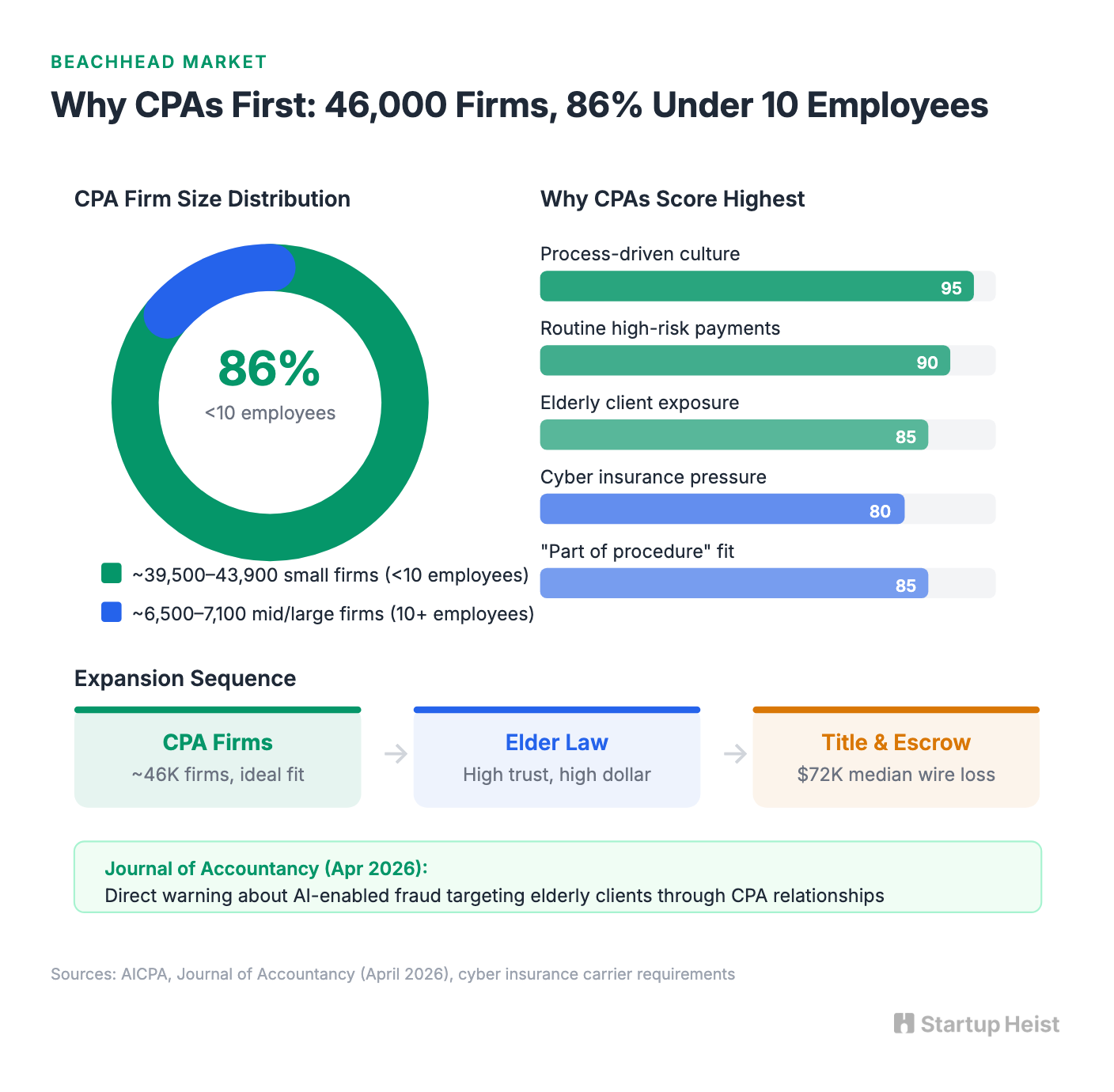
Cyber insurance requirements are tightening the screws from the other direction. By 2026, carriers are demanding documentation of controls: logs, policies, and proof, not checkbox answers on questionnaires. A verification tool that produces an audit trail positions directly against that pressure.
The sequence after CPAs: estate and elder-law practices (high trust, high-dollar instructions, similar client profiles), then boutique title and escrow firms (where median wire fraud loss is $72,000 per incident, though distribution channels run closer to bank workflows that can box out a standalone tool).
What to Build
The product is one idea: when a client asks you to do something risky, send them a trust link.
A staff member opens the dashboard, clicks "New Verification," and selects a reason: wire instruction, payment detail change, authority change, sensitive document release, large invoice approval, or other high-risk instruction. The system sends a branded SMS or email link. The client opens it on their phone, consents, and completes a guided flow as follows:

Unlock the Vault.
Join founders who spot opportunities ahead of the crowd. Actionable insights. Zero fluff.
“Intelligent, bold, minus the pretense.”
“Like discovering the cheat codes of the startup world.”
“SH is off-Broadway for founders — weird, sharp, and ahead of the curve.”






















